Difference Between Telnet and SSH

Telnet and Secure Shell, also known as SSH, are two different network protocols that have come into frequent use. In order to enhance communication, both of these network protocols are used to connect to remote servers; Telnet and SSH basically serve the same purpose. The main difference between the two basically lies in the level of security, which is the reason why SSH was able to suspend Telnet.
Telnet does not offer any security measures whatsoever, whereas SSH provides a security mechanism which helps users deal with anyone harbouring malicious or spiteful intentions. Another difference between the two is that the former sends the data in plain text, whereas the latter encrypts the data.
Telnet does not use any kind of authentication while people operating SSH have to use a public key. As compared to Telnet, SSH adds more overhead to the bandwidth, which is another reason why it is preferred these days, and has replaced Telnet in almost every kind of usage.
Instructions
-
1
Telnet
Telnet was not designed to work across a public network, which is the reason why it is not safe as there are different types of threats involved in an open network. Instead, it was designed primarily for private networks. This is the main reason why all the data, including passwords, is transmitted in plain text, making it extremely unsafe. Any person can intercept communication in this type of a network protocol, because it does not require any kind of authentication. Since the arrival of the SSH network protocol, Telnet has rapidly lost its popularity.
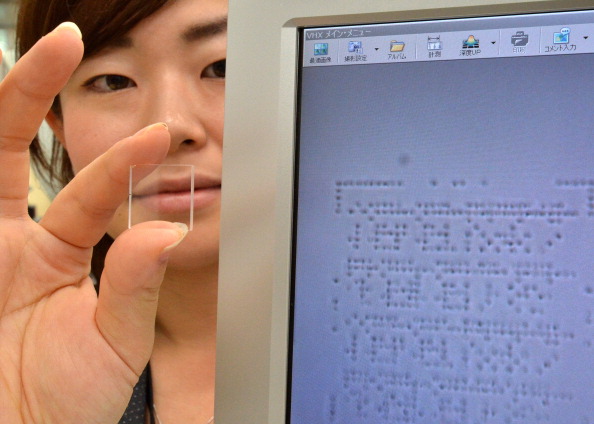
Image courtesy: gettyimages.com

-
2
SSH
To make room for the data of security mechanisms, each packet contains lesser data in SSH. This was a crucial security measure to be used in public networks. In order to cope with the security issues involved with Telnet, encryptions were used in SSH by its developers, in order to make it harder for other people to steal passwords or any other sensitive information.
SSH has also addressed the issue of authentication because it uses a public key to authenticate the source of the data. SSH has also solved the issue of the overhead of bandwidth, which was a major issue in the days when internet speeds were quite slow.
Image courtesy: gettyimages.com